Fortifying the Stack: Best Cybersecurity Software Tools for B2B Ecosystems
Advertisement
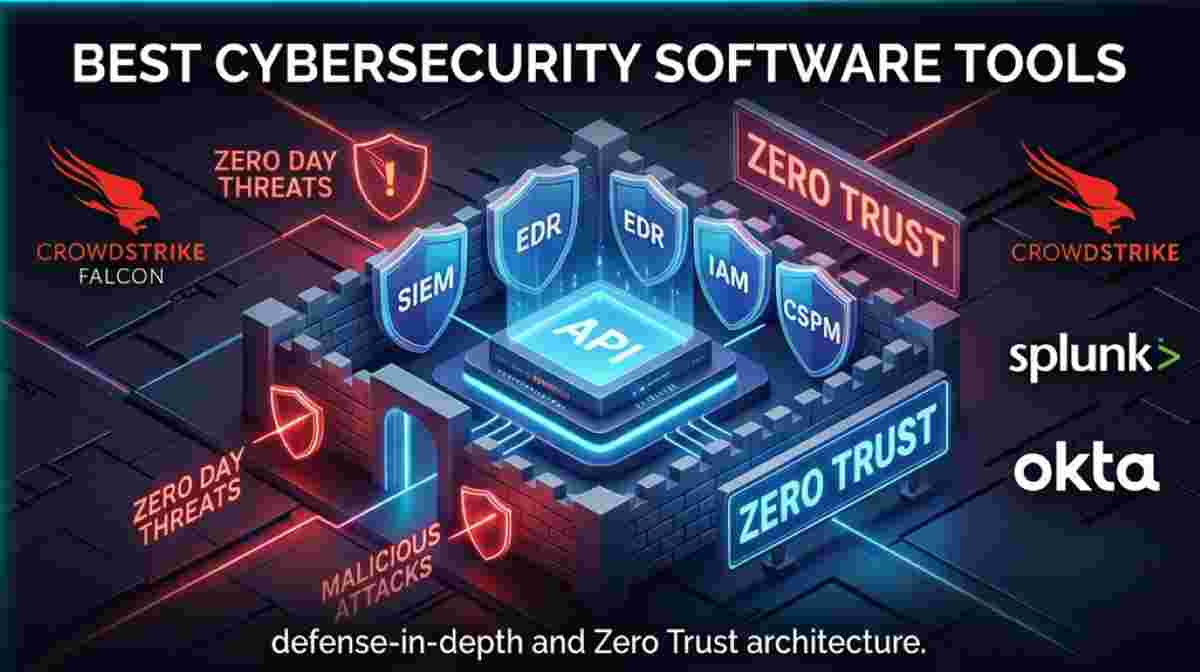
As enterprise perimeters dissolve into remote workforces and multi-cloud environments, traditional firewalls are no longer sufficient. Identifying the best cybersecurity software tools means adopting a Zero Trust architecture where every application, user, and device is continuously authenticated. For technical founders and CISOs, deploying advanced security tooling mitigates the devastating financial and reputational impacts of a data breach.
Structuring an enterprise defense strategy should closely follow the NIST Cybersecurity Framework (CSF), ensuring capabilities across Identify, Protect, Detect, Respond, and Recover functions. Additionally, global SaaS vendors must align their tooling with ISO/IEC 27001 standards for information security management. When evaluating the cryptographic strength managed by these tools (such as API keys and user passwords), engineers calculate Information Entropy to quantify resistance against brute-force attacks:
$E = \log_2(R^L)$
where $E$ is the entropy in bits, $R$ is the pool of possible characters, and $L$ is the length of the string. A higher entropy indicates an exponentially more secure system.
| Software Tool | Primary Category | Core SaaS Use Case | Deployment Model |
|---|---|---|---|
| CrowdStrike Falcon | EDR / XDR | Endpoint Threat Hunting | Cloud-Native Agent |
| Splunk Enterprise Security | SIEM | Log Aggregation & Analysis | On-Prem / Cloud |
| Palo Alto Prisma Cloud | CSPM / CNAPP | Multi-Cloud Compliance | Cloud-Native |
| Okta | IAM | Federated SSO Authentication | Cloud-Native |
| Tenable Nessus | Vulnerability Management | Infrastructure Patch Auditing | Hybrid |
| Wiz | CSPM | Agentless Cloud Risk Assessment | Cloud-Native API |
| Burp Suite Enterprise | DAST / AppSec | Automated API & Web App Testing | Self-Hosted / Cloud |
1. CrowdStrike Falcon
The CrowdStrike Falcon platform revolutionized Endpoint Detection and Response (EDR) by shifting the heavy lifting of threat detection to a unified cloud architecture. It replaces legacy antivirus systems that rely on outdated signature matching.
- AI-Powered Indicators of Attack (IoAs): Uses machine learning to analyze endpoint behavioral telemetry, stopping zero-day ransomware before it encrypts the local disk.
- Single Lightweight Agent: Operates at the kernel level with minimal CPU overhead, ensuring no performance degradation for developers compiling code.
- Threat Graph: A massive cloud-based graph database that correlates trillions of security events globally to rapidly identify distributed attacks.
2. Splunk Enterprise Security
Splunk is the industry heavyweight for Security Information and Event Management (SIEM). It ingests massive volumes of machine data from across the SaaS infrastructure, turning disparate logs into actionable security intelligence.
- Universal Forwarders: Lightweight agents that securely collect and transmit real-time log data from web servers, databases, and network switches into the Splunk indexers.
- Advanced Correlation Searches: Allows security analysts to write complex SPL (Search Processing Language) queries to detect advanced persistent threats (APTs) hiding in API traffic.
- Automated Playbooks (SOAR integration): Seamlessly integrates with Splunk Phantom to automatically quarantine compromised user accounts or block malicious IP ranges.
3. Palo Alto Networks Prisma Cloud
Prisma Cloud is a comprehensive Cloud-Native Application Protection Platform (CNAPP). It is essential for SaaS providers building microservices across AWS, Azure, and Google Cloud environments.
- Shift-Left Security: Integrates directly into IDEs and CI/CD pipelines to scan Infrastructure as Code (Terraform, Kubernetes manifests) for misconfigurations before deployment.
- Container Security: Continuously monitors Docker containers and serverless functions (like AWS Lambda) for known CVEs and unauthorized runtime behaviors.
- Microsegmentation: Enforces granular network policies based on workload identity rather than IP addresses, minimizing the blast radius of a compromised service.
4. Okta Workforce Identity
Okta is the leading Identity and Access Management (IAM) provider. By federating identities, it ensures that employees and B2B customers authenticate securely before accessing internal dashboards or CRM tools.
- Universal Directory: Provides a single, centralized view of all users, groups, and devices, easily syncing with legacy Active Directory or LDAP servers.
- Contextual Access Management: Evaluates the risk of a login attempt in real-time based on the user's IP, device posture, and geolocation before prompting for step-up MFA.
- Lifecycle Management: Automates the provisioning and de-provisioning of SaaS application access via SCIM when an employee is added or removed from the HRIS.
5. Tenable Nessus
Nessus is the gold standard for vulnerability scanning. It actively probes network infrastructure, operating systems, and web applications to identify missing patches and default configurations.
- Extensive Plugin Library: Backed by Tenable Research, it boasts the industry's lowest false-positive rate and updates its vulnerability signatures within 24 hours of a new zero-day disclosure.
- Authenticated Scanning: Uses provided credentials to log directly into servers via SSH or WMI to perform deep, registry-level vulnerability assessments.
- Compliance Auditing: Features built-in templates to automatically audit IT systems against specific regulatory benchmarks like HIPAA, PCI-DSS, and CIS Controls.
6. Wiz
Wiz has rapidly disrupted the cloud security landscape with its agentless, API-driven approach to Cloud Security Posture Management (CSPM). It provides 100% visibility into cloud environments in minutes without requiring DevOps teams to deploy code.
- Agentless Deep Scanning: Uses cloud provider APIs to take out-of-band snapshots of block storage, scanning for vulnerabilities, secrets, and malware without impacting live workloads.
- The Wiz Security Graph: Correlates network exposure, cloud entitlements (IAM), and vulnerabilities to prioritize the "toxic combinations" that pose the highest actual risk of breach.
- Data Security Posture Management (DSPM): Automatically discovers and classifies sensitive data (like PII or credit card numbers) residing in unencrypted S3 buckets or public databases.
7. Burp Suite Enterprise Edition
Developed by PortSwigger, Burp Suite is the definitive tool for dynamic application security testing (DAST) and penetration testing. It is critical for engineering teams validating the security of their proprietary SaaS web applications.
- Automated Vulnerability Scanner: Crawls modern single-page applications (SPAs) and complex API endpoints to discover SQL injection, Cross-Site Scripting (XSS), and SSRF vulnerabilities.
- OAST (Out-of-band Application Security Testing): Uses Burp Collaborator to detect asynchronous vulnerabilities where the attack payload triggers an external DNS or HTTP interaction rather than a direct response.
- CI/CD Integration: Allows QA teams to trigger automated security scans via REST APIs every time new code is committed to the main branch.
Frequently Asked Questions
What is the difference between EDR and SIEM?
Endpoint Detection and Response (EDR) operates at the device level, actively hunting for and blocking malicious processes executing on laptops or servers. A Security Information and Event Management (SIEM) system is a centralized aggregator that collects and correlates logs from the EDR, firewalls, and applications to give a holistic view of the entire network architecture.
How do cybersecurity tools integrate with CI/CD pipelines?
Modern cybersecurity tools "shift left" by integrating into CI/CD platforms like GitHub Actions or Jenkins. They automatically scan source code (SAST), software dependencies (SCA), and Infrastructure as Code (IaC) during the build phase, failing the deployment pipeline if critical vulnerabilities are detected before they reach production.
Why is CSPM necessary for cloud-native SaaS applications?
Cloud Security Posture Management (CSPM) tools like Wiz are necessary because public clouds (AWS, Azure) operate on a shared responsibility model. While the provider secures the physical hardware, the SaaS company is responsible for securing their configurations. CSPM tools automatically detect misconfigurations like public-facing databases, overly permissive IAM roles, and unencrypted storage volumes.
Advertisement