10 Best Free & Paid Syslog Servers for Windows & Linux
Advertisement
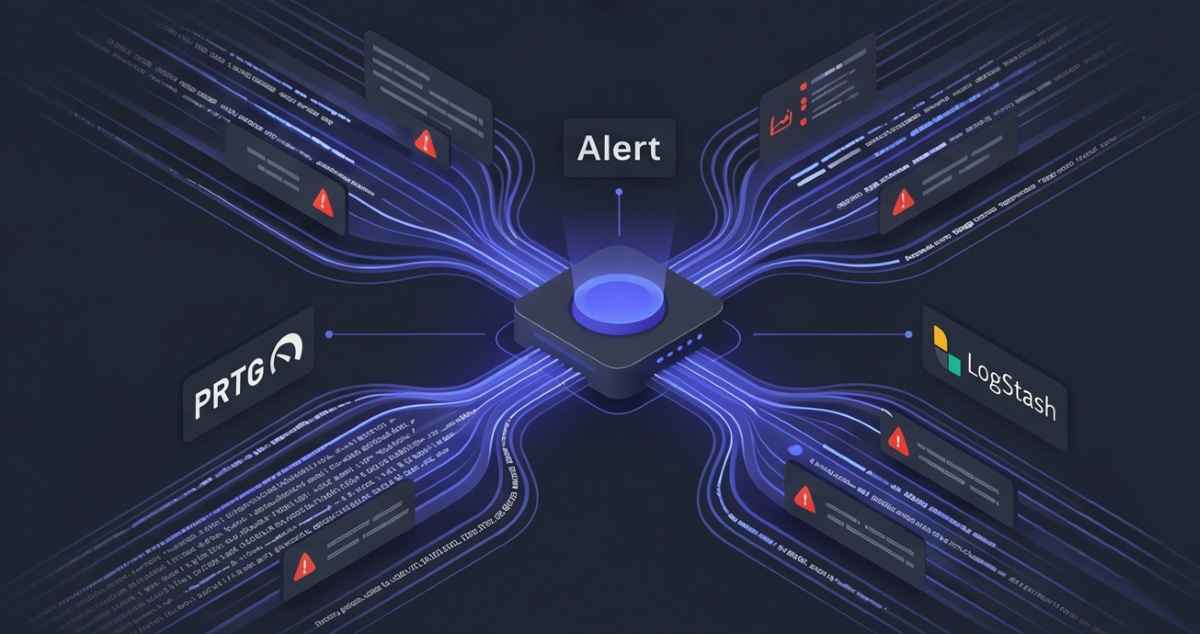
10 Best Syslog Servers for Windows and Linux
Whether you are managing a small office network on Windows or a massive enterprise Linux cluster, selecting the right log management tool is critical for both operational visibility and strict compliance reporting. We have reviewed the market's leading solutions to bring you the top ten free, open-source, and premium Syslog servers available today.
1. Paessler PRTG Syslog Server
Paessler PRTG is widely known for its comprehensive network monitoring capabilities, but its built-in Syslog Receiver sensor makes it an incredibly powerful, all-in-one logging solution for Windows environments.
- Unified Dashboard: Integrates your Syslog messages directly alongside your ping, bandwidth, and CPU sensors for complete network visibility.
- Customizable Alerting: Triggers instant email or SMS alerts when specific error codes or critical warning messages hit the Syslog server.
- Free Tier: Offers 100 sensors completely free forever, making it perfect for small businesses monitoring a few core routers and switches.
2. Logstash (Elastic Stack)
As the central data-processing pipeline of the famous ELK Stack (Elasticsearch, Logstash, Kibana), Logstash is a free, open-source giant. It is heavily favored by Linux administrators who need to process massive volumes of complex log data.
- Grok Filtering: Utilizes powerful grok filters to parse unstructured Syslog text into highly structured, searchable JSON fields.
- Universal Ingestion: Can simultaneously ingest Syslog messages, HTTP requests, and database events from virtually any source.
- External Reference: Explore the ELK ecosystem at Elastic.
3. SolarWinds Kiwi Syslog Server
Kiwi Syslog Server is an absolute staple in the IT industry. It is specifically designed to be lightweight, easy to set up on Windows, and highly affordable for mid-sized organizations.
- Automated Archiving: Automatically compresses, encrypts, and archives older logs to ensure you meet strict HIPAA or PCI compliance regulations without filling up your hard drive.
- Web-Based Access: Allows administrators to view real-time log streams from anywhere via a secure web portal.
- Rule-Based Actions: Can automatically run custom scripts or forward messages to another host based on specific log content.
4. Graylog
Graylog is an open-source log management platform that provides an exceptionally user-friendly alternative to the ELK stack. It is built for speed and is highly regarded for its brilliant search capabilities.
- Lightning-Fast Search: Allows engineers to comb through terabytes of Syslog data in milliseconds using a highly intuitive query language.
- Alerting Workflows: Features complex correlation engines that trigger alerts if a specific sequence of events happens (e.g., three failed logins followed by a massive database download).
- Sidecar Agents: Easily manages fleets of log collectors across both Windows and Linux endpoints from a centralized master node.
5. Splunk
Splunk is the undisputed heavyweight champion of enterprise log management and Security Information and Event Management (SIEM). If you have an enormous budget and need unparalleled analytics, Splunk is the answer.
- Machine Data Indexing: Ingests everything—Syslogs, custom application logs, web traffic, and metrics—creating a highly searchable data lake.
- AI & Machine Learning: Uses predictive analytics to automatically identify anomalous network behavior that human operators would miss.
- External Reference: See their enterprise solutions at Splunk.
6. Site24x7 Server Monitoring
Site24x7 offers a cloud-based approach to Syslog management. It is ideal for distributed teams that do not want to host or maintain their own on-premise log storage infrastructure.
- Zero Maintenance: Because log storage and processing happen in the cloud, you never have to worry about provisioning more local hard drives.
- AI-Powered Log Analysis: Automatically categorizes and parses standard Syslog formats, recognizing critical errors without manual rule creation.
- Hybrid Monitoring: Consolidates Syslogs from local Windows servers, Cisco routers, and AWS instances into one unified view.
7. ManageEngine EventLog Analyzer
EventLog Analyzer acts as both a Syslog server and a comprehensive SIEM tool. It is particularly strong in its ability to generate audit-ready compliance documentation instantly.
- Pre-Built Compliance Reports: Features out-of-the-box reporting templates for GDPR, SOX, HIPAA, and PCI DSS compliance.
- Agentless Collection: Pulls logs natively from Windows and Linux devices without requiring proprietary agents to be installed on your network hardware.
- Threat Intelligence: Cross-references incoming Syslog data against global threat feeds to instantly identify malicious IP addresses interacting with your network.
8. Fluentd
Fluentd is an open-source data collector that unifies data collection and consumption. It is heavily utilized in modern, containerized environments like Docker and Kubernetes.
- Unified Logging Layer: Acts as an intermediary layer that standardizes Syslogs and routes them to multiple backend systems (like MongoDB, Elasticsearch, or AWS S3) simultaneously.
- Low Footprint: Written in C and Ruby, it requires very little system memory, making it perfect for deployment on lightweight Linux nodes.
- Massive Plugin Ecosystem: Features over 500 community-built plugins to connect virtually any data source to any destination.
9. ManageEngine Log360
While EventLog Analyzer is a core component, Log360 expands the capability into a full-scale enterprise SIEM. It provides deep security analytics on top of standard Syslog collection.
- Active Directory Integration: Correlates network Syslog events directly with Windows Active Directory changes to catch insider threats.
- User Entity Behavior Analytics (UEBA): Profiles normal user behavior and alerts administrators if an employee suddenly downloads gigabytes of data at 3:00 AM.
- Incident Management: Includes built-in ticketing to assign investigations to specific security analysts when a critical log triggers an alarm.
10. Datadog Log Management
Datadog provides an exceptionally powerful, cloud-native log management platform that allows you to dynamically ingest all Syslogs but only index the ones you actually need, saving massive amounts of money.
- Logging Without Limits™: Ingest all your Syslog data into a low-cost archive, and only pay to index and search the logs that are actively needed for troubleshooting.
- Seamless Correlation: Connects a slow network request in your APM trace directly to the specific router Syslog that shows dropped packets.
- Live Tail: Watch your Syslog stream across thousands of servers in real-time right from your browser, exactly as if you were SSH'd into the machine.
FAQs
What is the Syslog protocol?
Syslog is a standard protocol used by network devices (like routers, switches, and firewalls) and Linux/Unix servers to send event messages to a central logging server. It uses a specific format that includes a timestamp, a severity rating (e.g., Error, Warning, Info), and the actual event message.
Why can't I just view logs locally on each device?
In a corporate network, you might have hundreds of devices. If a network outage occurs, logging into each device individually to read text files takes too long. Furthermore, if a hacker breaches a server, they usually delete the local logs to cover their tracks. A central Syslog server securely stores these logs away from the compromised machine.
What is a SIEM, and how does it relate to a Syslog server?
A Syslog server simply collects and stores log messages. A Security Information and Event Management (SIEM) tool takes those logs, analyzes them using AI and threat intelligence, and actively alerts security teams if the log patterns suggest a cyberattack is occurring.
Advertisement