10 Best TeamViewer Alternatives for Enterprise (2026)
Advertisement
10 Best TeamViewer Alternatives for Enterprise IT (2026)
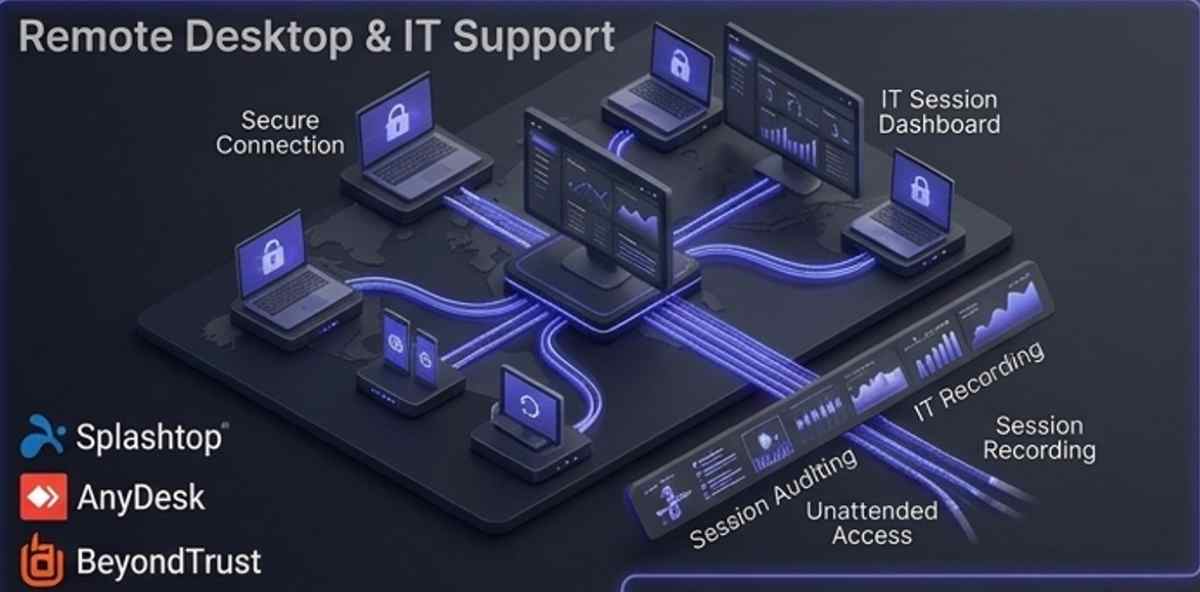
Modern remote monitoring and management (RMM) requires strict adherence to global cybersecurity frameworks. When evaluating enterprise remote desktop software, CTOs must ensure the platform aligns with the telework and remote access guidelines defined by the NIST Computer Security Resource Center. Additionally, platforms must utilize standardized, highly audited cryptographic tunneling protocols verified by standard-setting organizations such as the IEEE to prevent unauthorized interception of corporate telemetry and session data.
The mathematical foundation of secure remote sessions relies on establishing impenetrable encryption keys before any visual data or file transfers are executed. For instance, the entropy ($E$) of a session's cryptographic key can be modeled as $E = \log_2(R^L)$, where $R$ represents the character pool size and $L$ denotes the key length. Maximizing this entropy alongside mandatory AES-256 bit encryption ensures that enterprise remote access gateways remain mathematically immune to brute-force decryption, safeguarding proprietary data during active support sessions.
| Tool Name | Best For | Deployment Model |
|---|---|---|
| Splashtop Enterprise | High-Performance Streaming & IT Support | Cloud / On-Premise |
| AnyDesk | Low-Latency Connections & Ad-hoc Support | Cloud / On-Premise |
| BeyondTrust | Privileged Access Management (PAM) | Cloud / Appliance |
| ConnectWise ScreenConnect | Advanced IT Scripting & MSPs | Cloud / Self-Hosted |
| NinjaOne | Unified RMM & Endpoint Patching | Cloud-Native (SaaS) |
| Zoho Assist | Helpdesk Integration & SMBs | Cloud-Native (SaaS) |
| RemotePC | Scalable Telecommuting Deployments | Cloud-Native (SaaS) |
| RealVNC Connect | Cross-Platform Developer Environments | Cloud / On-Premise |
| Microsoft Remote Desktop | Native Windows Infrastructure | OS-Integrated / Hybrid |
| Dameware Remote Everywhere | Deep Diagnostics & Active Directory | Cloud-Native (SaaS) |
1. Splashtop Enterprise
Splashtop Enterprise has emerged as a dominant force in the remote access market, offering an exceptional balance of high-fidelity screen streaming and rigorous administrative controls. It is particularly favored by IT departments managing resource-heavy software on remote workstations.
- High-Fidelity Streaming: Capable of delivering 4K resolution at 60 frames per second, making it ideal for remotely operating graphic-intensive applications without noticeable latency.
- Granular Privilege Management: Allows IT administrators to implement role-based access control (RBAC), ensuring technicians only access specific endpoints based on active directory group policies.
- Product Link: Discover their advanced enterprise IT support features directly at Splashtop.
2. AnyDesk
AnyDesk is renowned for its proprietary DeskRT video codec, which ensures buttery-smooth remote desktop sessions even in low-bandwidth environments. Its incredibly lightweight client makes it a top choice for spontaneous IT support.
- Military-Grade Security: Secures all remote sessions using standard TLS 1.2 technology and RSA 2048 asymmetric key exchange encryption to prevent man-in-the-middle attacks.
- Custom Client Generation: Enables IT departments to deploy a custom-branded executable pre-configured with corporate proxy settings and security policies, removing user friction during setup.
- Unattended Access: Allows seamless connection to headless servers and remote IoT devices through password-protected, persistent installation modules.
3. BeyondTrust Remote Support
BeyondTrust approaches remote access through the lens of Privileged Access Management (PAM). It is the premier solution for highly regulated enterprise environments, such as finance and healthcare, where auditability is strictly mandated.
- Credential Injection: Allows technicians to securely elevate privileges on a remote machine using administrative credentials vaulted in the backend, completely hiding the plaintext password from the technician.
- Immutable Audit Trails: Automatically records high-definition video logs and terminal commands for every remote session, storing them in a tamper-proof vault for regulatory compliance.
- Appliance-Based Architecture: Can be deployed via physical or virtual appliances, ensuring sensitive remote access traffic never traverses public, multi-tenant cloud servers.
4. ConnectWise ScreenConnect
Formerly known as ConnectWise Control, ScreenConnect is a heavily extensible platform utilized by Managed Service Providers (MSPs) and internal IT teams that require deep scripting and background remediation capabilities.
- Backstage Mode: Provides technicians with full access to the Windows command prompt, PowerShell, and registry editor of the remote device without interrupting the active user's desktop session.
- Advanced Trigger System: Automates IT workflows by executing predefined scripts or sending alerts when specific endpoint conditions are met (e.g., a service crashes or disk space falls below a threshold).
- Deep PSA Integrations: Acts as the central remote tool for the ConnectWise ecosystem, seamlessly pushing session notes and time-logs directly into Professional Services Automation platforms.
5. NinjaOne
NinjaOne transcends standard remote control by offering a unified Remote Monitoring and Management (RMM) platform. It provides a single pane of glass for remote access, automated patch management, and endpoint security.
- Native Remote Tools: Integrates custom-built remote access directly into the endpoint management dashboard, allowing 1-click connections without launching secondary applications.
- Background Remediation: Equips IT administrators with a suite of background tools to manage services, kill processes, and deploy software updates completely silently.
- Automated IT Workflows: Enables the creation of complex automation scripts that can be pushed to thousands of remote endpoints simultaneously, ensuring global infrastructure hygiene.
6. Zoho Assist
Zoho Assist provides a highly accessible, cloud-native remote support platform that excels in Helpdesk integrations. It is engineered to reduce the friction of supporting non-technical remote workers and external clients.
- Web-Based Technician Console: Allows IT support staff to initiate and manage complex remote sessions entirely from a web browser without requiring a dedicated technician client installation.
- Voice and Video Chat: Integrates native VoIP and video communication directly within the remote session window, eliminating the need to run parallel meeting software while troubleshooting.
- Unattended Deployment: Facilitates mass deployment of unattended access agents via Group Policy Object (GPO) or native integration with major endpoint management suites.
7. RemotePC by IDrive
RemotePC offers a straightforward, highly scalable remote desktop solution that is cost-effective for enterprise telecommuting deployments. It provides robust performance without the complexity of traditional RMM platforms.
- Always-On Enterprise Access: Allows IT to configure thousands of office workstations for secure, always-on access, enabling employees to connect from any remote location globally.
- Endpoint Scalability: Features an Enterprise deployment console that allows centralized management of user provisioning, role assignments, and active session monitoring across the entire organization.
- Blank Screen & Lock: Enhances corporate privacy by allowing the remote user to blank the physical host monitor and lock the local keyboard/mouse during a session.
8. RealVNC Connect
RealVNC Connect leverages the robust Virtual Network Computing (VNC) protocol to deliver unparalleled cross-platform compatibility. It is widely used by engineering and development teams working across diverse operating systems.
- True Cross-Platform Support: Connects seamlessly between Windows, macOS, Linux, and Raspberry Pi environments, making it ideal for managing diverse server rooms and developer workstations.
- Direct Enterprise Connectivity: Offers both cloud-brokered connections and direct peer-to-peer TCP connections, providing flexibility for isolated corporate networks with strict firewall rules.
- High-Security Deployments: Secures sessions with up to 256-bit AES encryption and integrates seamlessly with enterprise identity providers via SAML 2.0.
9. Microsoft Remote Desktop (RDS)
Microsoft Remote Desktop Services (RDS) remains a foundational tool for enterprises deeply embedded in the Microsoft infrastructure. It utilizes the proprietary Remote Desktop Protocol (RDP) for native integration.
- OS-Level Integration: Because RDP is built directly into the Windows operating system, it requires no third-party agent installation on target machines, minimizing endpoint bloat.
- RemoteApp Publishing: Allows IT to virtualize and publish specific applications to remote users rather than presenting a full desktop environment, streamlining access to corporate CRM or ERP software.
- Active Directory Synergy: Leverages existing Active Directory infrastructures perfectly for seamless authentication, session brokering, and Group Policy enforcement.
10. Dameware Remote Everywhere
Built by SolarWinds, Dameware Remote Everywhere (DRE) is a cloud-based remote support solution designed to provide deep system diagnostics and rapid troubleshooting for IT helpdesks.
- Advanced Diagnostic Tools: Provides the technician with an instant snapshot of the remote machine's health, including CPU utilization, event logs, and update status, before the screen sharing even begins.
- Pre-Session Chat: Allows technicians to initiate a secure chat with the end-user to understand the issue and request elevated permission before taking over the desktop.
- Secure Session Reporting: Generates comprehensive, exportable reports detailing connection times, chat transcripts, and system changes made during the session for ITSM compliance auditing.
FAQs
What makes an enterprise remote desktop tool secure?
Enterprise-grade remote access platforms rely on a Zero Trust architecture. This means implementing end-to-end AES-256 encryption, enforcing Multi-Factor Authentication (MFA) via SAML/SSO integrations, and maintaining immutable audit logs of every session. Furthermore, advanced tools require device posture checks before allowing the connection to initiate.
What is the difference between attended and unattended access?
Attended access requires the end-user to be physically present at the remote machine to generate a code or accept a prompt before the IT technician can connect. Unattended access utilizes a securely installed background service, allowing an administrator to connect to servers or employee workstations at any time, which is critical for out-of-hours maintenance and patching.
Can TeamViewer alternatives bypass corporate firewalls safely?
Yes. Modern solutions utilize outbound TCP/UDP connections to centralized cloud brokering servers (typically over port 443). Because the remote machine initiates an outbound connection to the broker, it effectively traverses NAT routers and strict corporate firewalls without requiring IT to open vulnerable inbound ports or configure manual port forwarding.
Advertisement