The Convergence of ITSM and Cybersecurity: A Guide to SecOps
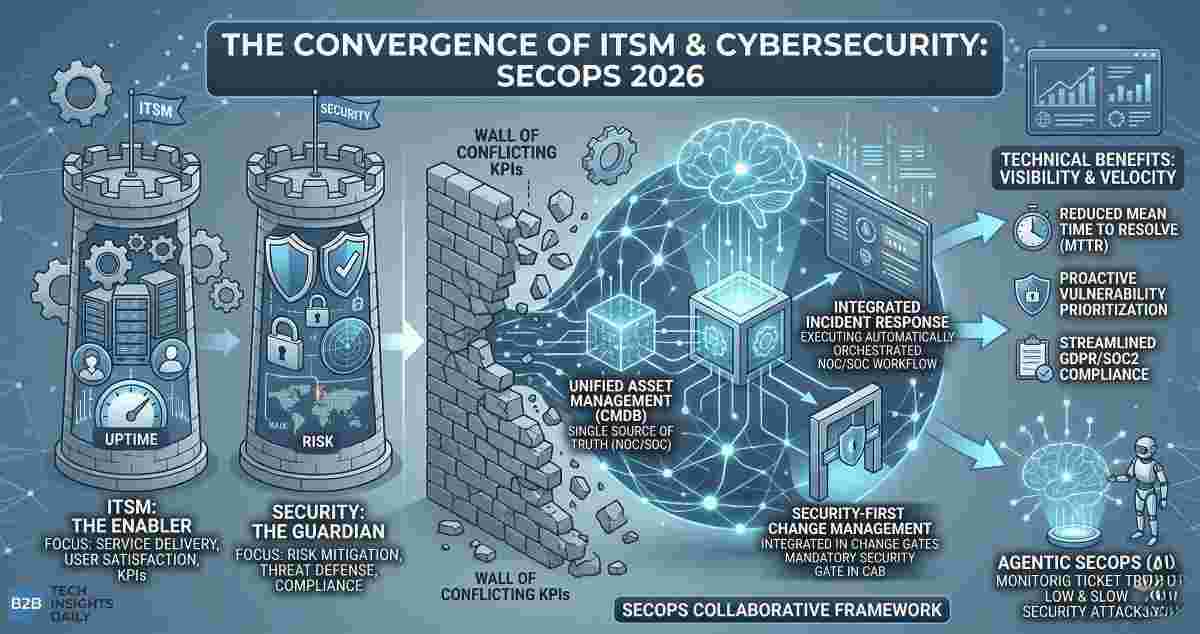
In the traditional enterprise, IT Service Management (ITSM) and Cybersecurity have operated as two distinct islands. ITSM was the "Enabler," focused on uptime, service delivery, and user satisfaction. Cybersecurity was the "Guardian," focused on risk, compliance, and threat mitigation. However, as the threat landscape evolves in 2026, this siloed approach is no longer sustainable.
The convergence of these two disciplines is known as SecOps—a collaborative framework that integrates security into every phase of the IT service lifecycle.
I. The "Wall" is Falling: Why ITSM and Security Must Merge
Historically, the friction between IT and Security was a byproduct of conflicting KPIs. IT wanted to push changes fast to meet SLAs; Security wanted to slow down to perform audits.
The reality is that a service cannot be "available" if it is compromised. By integrating security protocols directly into the ITSM workflow, organizations eliminate the "security as an afterthought" bottleneck. This convergence ensures that security is baked into the CMDB (Configuration Management Database), Change Management, and Incident Response from day one.
II. The Core Pillars of a SecOps Strategy
Integrating these departments requires aligning three technical pillars:
- Unified Asset Management: You cannot secure what you cannot see. A modern CMDB must serve as the "Single Source of Truth" for both the NOC (Network Operations Center) and the SOC (Security Operations Center).
- Integrated Incident Response: When a security breach occurs, it is technically an "Incident." By using ITSM platforms to orchestrate security playbooks, teams can respond with the same rigor and documentation used for hardware failures.
- Security-First Change Management: Every patch or update is a potential vulnerability. SecOps ensures that security assessments are a mandatory gate in the Change Advisory Board (CAB) process.
III. Technical Benefits: Visibility and Velocity
- Reduced Mean Time to Resolve (MTTR): With integrated tools, a security alert can automatically trigger an ITSM ticket with full asset context, saving the SOC team hours of manual investigation.
- Proactive Vulnerability Management: By linking vulnerability scanners with the ITSM service desk, patches are automatically prioritized based on the business criticality of the asset.
- Streamlined Compliance: Integrated logging between ITSM and SIEM (Security Information and Event Management) tools makes auditing for HIPAA, GDPR, or SOC2 a continuous process rather than a quarterly panic.
IV. Moving Toward the 2026 Security Maturity Model
Modern enterprises are now adopting "Agentic SecOps." This involves using AI agents that monitor ITSM ticket trends to identify "low and slow" security attacks that might look like routine technical glitches to a human technician.
FAQs
ITSM is the broad discipline of managing IT services. SecOps is the specific sub-discipline and cultural shift that integrates security practices and tools directly into the ITSM and IT operations workflow.
By automating security checks within the service desk, users get their requests (like access to a new application) fulfilled faster because the security validation happens in real-time through automated workflows rather than manual approvals.
Absolutely. For smaller teams, SecOps starts with tool consolidation—using an ITSM platform that has native security features or integrates seamlessly with a basic SIEM, ensuring that security is handled as part of daily IT maintenance.
For further reading on integrating security within IT service frameworks, refer to the official CISA Cybersecurity Best Practices .