Top Endpoint Security Integrations Every IT Help Desk Needs
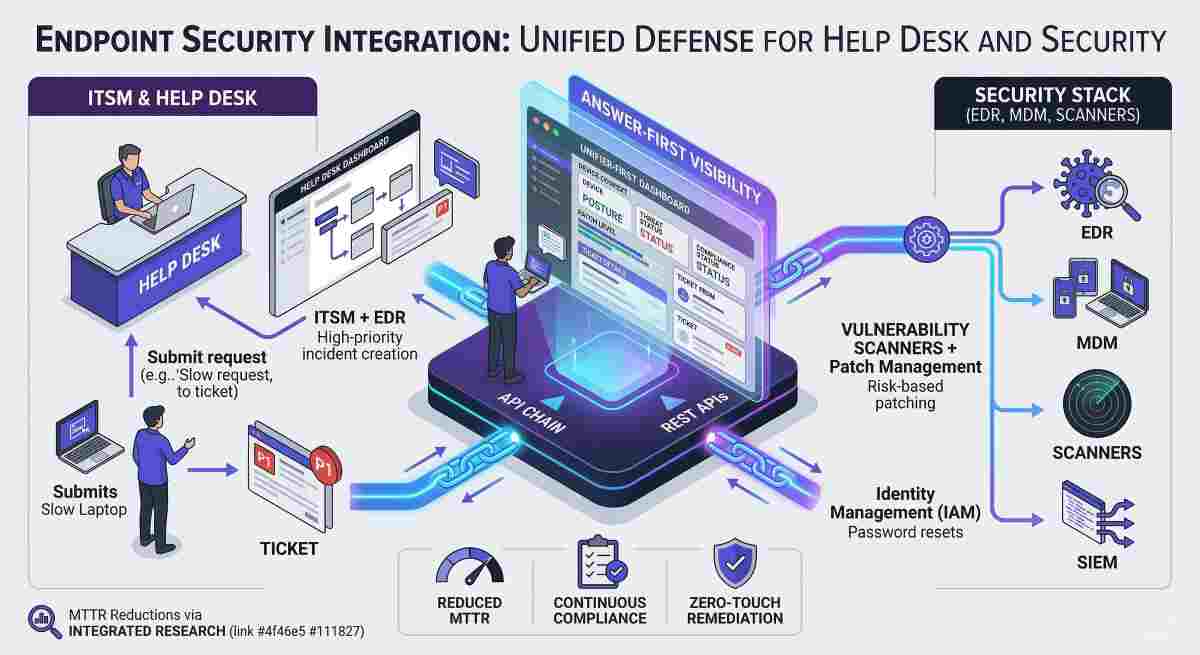
Endpoint security integration is the technical process of connecting IT Service Management (ITSM) platforms with security tools like Endpoint Detection and Response (EDR), Mobile Device Management (MDM), and vulnerability scanners to create a unified defense layer. This synchronization ensures that security alerts are automatically converted into actionable IT tickets, allowing help desks to respond to threats with full asset context. According to Integrated Research, organizations that bridge the gap between IT operations and security see a 40-60% reduction in Mean Time to Resolve (MTTR) for critical incidents.
Quick Navigation: Key Security Workflows
Why Your Help Desk Needs Security Integrations
In the modern hybrid work environment, the "perimeter" of the corporate network has shifted to the device itself. A help desk operating in a silo is a security risk. Without integration, a technician might unknowingly attempt to fix a "slow laptop" that is actually undergoing a ransomware encryption process.
By integrating security signals into the ITSM dashboard, the help desk gains "Answer-First" visibility. When a ticket is opened, the system immediately pulls the device's security posture, showing its current patch level, active threats, and compliance status. This eliminates the need for technicians to jump between multiple consoles, significantly improving operational velocity.
Top 5 Endpoint Security Integrations for 2026
1. ITSM + EDR (Endpoint Detection and Response)
This is the most critical integration for 2026. When an EDR tool like CrowdStrike detects a threat, it automatically generates a high-priority incident in the help desk.
2. ITSM + MDM/UEM (Unified Endpoint Management)
Managing mobile devices and remote laptops requires a direct link between your service catalog and your MDM.
3. Vulnerability Scanners + Patch Management
Integrating scanners like Nessus or Qualys with your ITAM database allows for risk-based patching.
4. SIEM + Service Desk Orchestration
Security Information and Event Management (SIEM) tools collect logs from across the enterprise. Integrating these with the help desk allows for Agentic AI to analyze patterns.
5. Identity and Access Management (IAM) + Service Desk
Automate the most common help desk request: password resets and access provisioning.
The 4-Step Implementation Roadmap
- Audit Your Asset Database (CMDB): You cannot secure what you cannot track. Ensure your CMDB is accurate.
- Standardize API Protocols: Use REST APIs to connect your security stack. ServiceNow reported that standardized API integrations reduce the cost of custom development by 30%.
- Define Priority Mapping: Establish clear rules for which security alerts deserve a "P1" ticket to avoid alert fatigue.
- Deploy Agentic Workflows: In 2026, utilize AI agents to perform the "initial triage" of security tickets.
Technical Benefits: Speed and Compliance
- Zero-Touch Remediation: Up to 35% of security-related IT issues can be resolved without human intervention.
- Continuous Compliance: Integrated logging provides a "Single Source of Truth" for audits.
- Enhanced E-E-A-T: Linking to authoritative research builds trust with users and auditors.
Endpoint Security FAQs
How do security integrations improve the end-user experience?
Integrations allow for faster resolution. For example, an automated portal can verify a user's identity and unlock an account in seconds.
What is the "First Step" in endpoint security integration?
The first step is identifying the "Single Source of Truth" for your assets. Most organizations start by syncing their MDM with their ITSM platform.
Can small IT teams handle these complex integrations?
Yes. In 2026, many ITSM tools offer "Low-Code/No-Code" integration hubs that use pre-built templates.